ECS Linux云服务器tengine结合lua防御cc攻击案例
Web站点运行的过程中非常难免的会遭遇各种各样的攻击,不管是有意的攻击(竞争对手的恶意攻击),还是无意的攻击(黑客新手的练习)都是防不胜防的,这里给出一个tengine结合lua防御cc攻击的案例
一、下载和安装tengine与luajit
tengine下载地址http://tengine.taobao.org/ 选择稳定的安装包下载编译安装即可这里用的包是tengine-2.1.1.tar.gz
luajit下载地址http://luajit.org/download.html 选择稳定的安装包下载编译安装即可这里用的包是LuaJIT-2.0.4.tar.gz
安装的步骤如下
1、安装环境需要的基础文件
yum install zlib zlib-devel openssl openssl-devel pcre pcre-devel -y
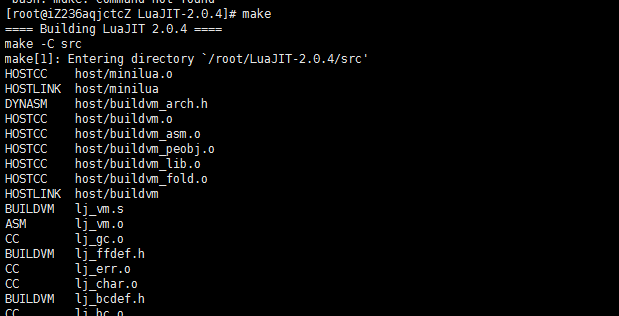
2、下载和安装LuaJIT-2.0.4.tar.gz
#wget http://luajit.org/download/LuaJIT-2.0.4.tar.gz
#tar zxvf LuaJIT-2.0.4.tar.gz
#cd LuaJIT-2.0.4
#make
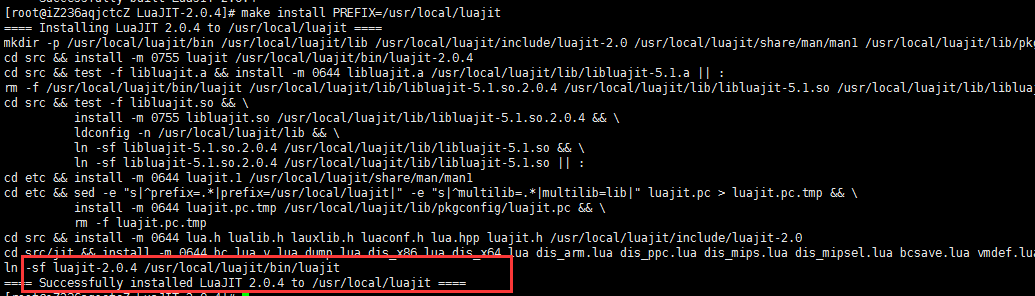
#make install PREFIX=/usr/local/luajit
出现以下红框信息显示安装成功了,可以进行下一步了
3、下载和安装tengine-2.1.1.tar.gz
#wget http://tengine.taobao.org/download/tengine-2.1.1.tar.gz
#tar zxvf tengine-2.1.1.tar.gz
#cd tengine-2.1.1
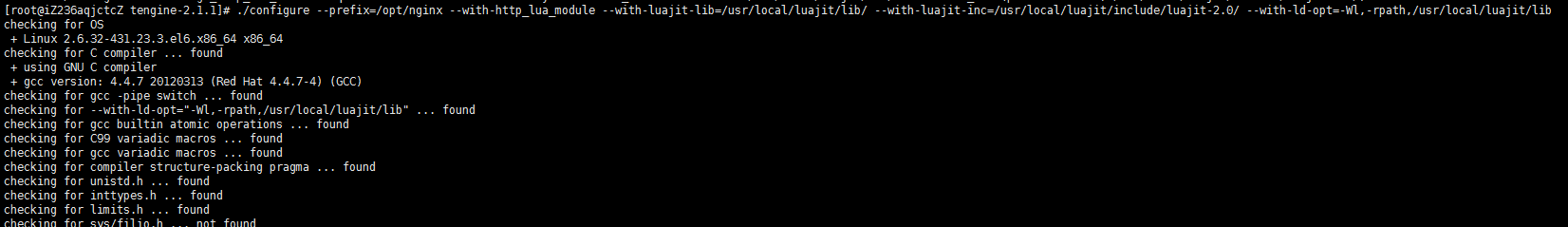
#./configure –prefix=/opt/nginx –with-http_lua_module –with-luajit-lib=/usr/local/luajit/lib/ –with-luajit-inc=/usr/local/luajit/include/luajit-2.0/ –with-ld-opt=-Wl,-rpath,/usr/local/luajit/lib
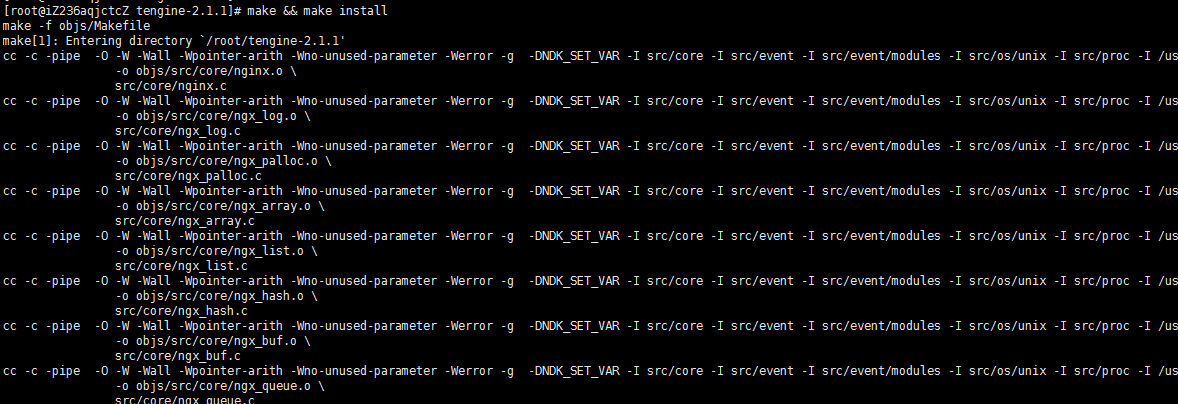
#make && make install
二、下载和配置ngx_lua_waf
nginx下常见的开源waf有mod_security、naxsi、ngx_lua_waf这三个,ngx_lua_waf性能高和易用性强,基本上零配置,而且常见的攻击类型都能防御,是比较省心的选择
解压缩
#unzip master.zip
挪到nginx的目录下
#mv ngx_lua_waf-master /opt/nginx/conf/
重命名一下
#cd /opt/nginx/conf/
#mv ngx_lua_waf-master waf
修改ngx_lua_waf配置文件适应当前的nginx环境,修改以下文件的三行即可(修改/opt/nginx/conf/waf下的config.lua文件,将RulePath和logdir改为实际的目录:)
# cat /opt/nginx/conf/waf/config.lua|head -n3
RulePath = “/opt/nginx/conf/waf/wafconf/”
attacklog = “on”
logdir = “/opt/nginx/logs/waf”
三、修改tengine的配置文件应用ngx_lua_waf
在nginx.conf的http段添加
lua_package_path “/opt/nginx/conf/waf/?.lua”;
lua_shared_dict limit 10m;
init_by_lua_file /opt/nginx/conf/waf/init.lua;
access_by_lua_file /opt/nginx/conf/waf/waf.lua;
启动tengine–nginx服务
# /opt/nginx/sbin/nginx -t
the configuration file /opt/nginx/conf/nginx.conf syntax is ok
# /opt/nginx/sbin/nginx -s reload
四、测试攻防的效果
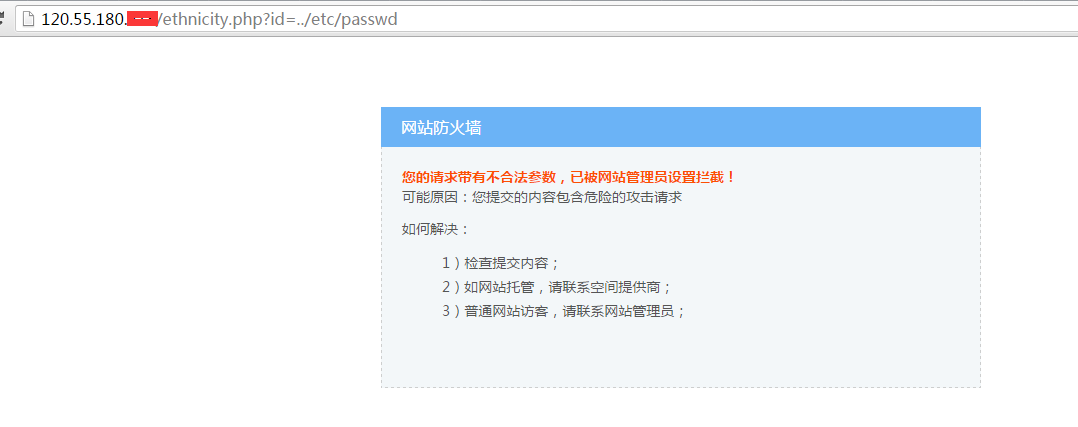
任意文件读取:
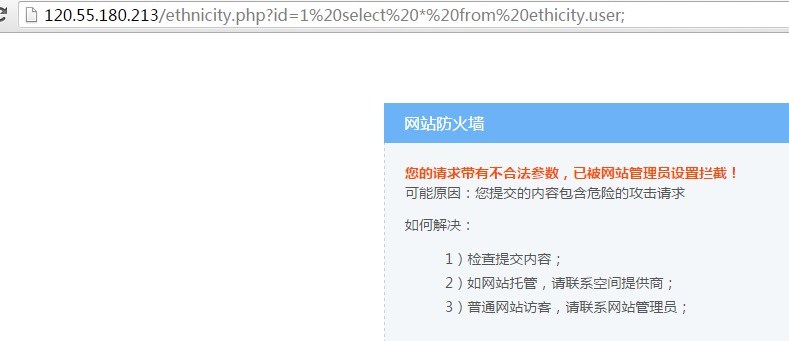
sql注入:

 QQ咨询
QQ咨询